Security teams do not struggle because of a lack of tools. The real problem sits somewhere else. Data arrives from everywhere, but context often arrives late. Alerts stack up while analysts try to determine what actually matters.
Modern SOC environments collect huge amounts of data. Endpoint signals, identity events, network logs, cloud activity. The challenge lies in turning that noise into meaningful detection. Threat intelligence plays a quiet but decisive role here.
Integrating threat intelligence into CrowdStrike NG-SIEM helps close that gap. Instead of analysing alerts in isolation, analysts gain context drawn from known attacker infrastructure, behavioural indicators and campaign patterns. Signals begin to carry meaning. Detection becomes faster. Investigation becomes clearer.
For organisations already relying on CrowdStrike’s ecosystem, adding structured intelligence into the NG-SIEM environment can significantly sharpen visibility across the security stack.
Why Threat Intelligence Matters Inside Modern SIEM Environments
Security operations often treat intelligence as a separate feed. Indicators arrive through external portals or standalone tools. Analysts then manually reference them during investigations. That separation slows everything down.
Threat intelligence becomes far more valuable when it lives inside the detection workflow itself. When data and intelligence interact directly, the SIEM platform begins to recognise patterns that resemble known attacks.
CrowdStrike NG-SIEM operates as a cloud-native analytics platform capable of taking vast telemetry streams from endpoints, identity systems and cloud workloads. On its own, this telemetry provides behavioural visibility. However, once intelligence feeds enrich that data, signals become far easier to prioritise.
Instead of investigating every suspicious domain or IP address, analysts can immediately see whether the activity aligns with known malicious infrastructure or adversary campaigns.
The effect is subtle but very important. Detection improves without adding operational overhead.
Understanding the Role of CrowdStrike NG-SIEM in the Security Stack
Traditional SIEM platforms relied heavily on log collection and rule matching. Many still struggle with scalability and context correlation.
CrowdStrike’s NG-SIEM approach differs slightly. The platform combines large scale telemetry ingestion with advanced analytics and threat intelligence built around the Falcon ecosystem.
It allows organisations to correlate:
- Endpoint telemetry
- Identity signals
- Cloud workload activity
- Third-party log sources
Once telemetry flows into the platform, analytics models and correlation rules evaluate suspicious patterns. Yet those signals become far more powerful when enriched with intelligence feeds. This is precisely where integrating threat intelligence into CrowdStrike NG-SIEM strengthens the overall detection strategy.
Instead of reacting to alerts, the platform begins recognising attacker infrastructure and behaviour in near real time.
The Practical Impact of Integrating Threat Intelligence
Security leaders often ask what changes after intelligence integration. The answer is less about new alerts and more about improved clarity.
Threat intelligence feeds usually include indicators like malicious domains, command and control infrastructure, malware hashes and attacker tooling patterns. When these indicators appear within NG-SIEM telemetry streams, the system can immediately flag the activity as potentially malicious.
More importantly, intelligence feeds also include contextual information. This may describe the threat actor, campaign objective or malware family involved. During an investigation, analysts gain instant context around the alert. That reduces guesswork.
A domain query linked to a ransomware campaign tells a different story than a domain associated with low level phishing activity. Intelligence allows the SOC to prioritise accordingly.
How Threat Intelligence Integrates into CrowdStrike NG-SIEM
The integration process does not rely on a single feed or mechanism. Instead, it combines multiple intelligence sources across the detection pipeline. Before intelligence becomes actionable, it passes through several stages inside the detection workflow.
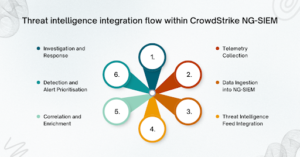
-
Telemetry Collection
Endpoint agents, identity providers, cloud services and network tools generate data. CrowdStrike Falcon sensors collect endpoint data while additional connectors ingest logs from external sources.
-
Data Ingestion into NG-SIEM
All data streams flow into the NG-SIEM analytics engine. This layer normalises the incoming data to ensure consistent event analysis across environments.
-
Threat Intelligence Feed Integration
External intelligence feeds, commercial sources and CrowdStrike’s own intelligence data are ingested into the system. These feeds include indicators such as malicious IP addresses, domains, hashes and attacker infrastructure.
-
Correlation and Enrichment
The NG-SIEM engine compares telemetry signals against intelligence indicators. Events matching known threat indicators are automatically enriched with contextual data.
-
Detection and Alert Prioritisation
When suspicious behaviour aligns with threat intelligence, detection rules elevate the alert severity. Analysts receive signals that already contain campaign context.
-
Investigation and Response
Analysts examine enriched alerts, identify the attack path and trigger response actions. Because the event already includes threat context, investigation time reduces significantly.
This workflow highlights the real value of Integrating Threat Intelligence into CrowdStrike NG-SIEM. Intelligence is not stored separately. It actively shapes how detections are prioritised and investigated.
Key Benefits Security Teams Experience
Threat intelligence integration tends to reshape how SOC teams handle daily operations. Several improvements emerge once intelligence feeds operate within the SIEM environment.
-
Faster detection of known adversaries
Threat actors reuse infrastructure more often than expected. Domains, hosting providers, malware signatures, and command servers frequently appear across multiple campaigns.
When intelligence feeds track those indicators, NG-SIEM can detect related activity almost instantly. Analysts no longer need to manually verify whether an indicator is malicious.
-
Reduced alert fatigue
Alert fatigue remains a persistent SOC problem. Many alerts trigger based purely on suspicious behaviour patterns, not confirmed malicious activity.
Threat intelligence introduces an additional layer of verification. Alerts that match known malicious infrastructure receive higher priority. Benign or low risk anomalies become easier to filter. This dramatically improves signal quality.
-
Improved investigation context
Security investigations often stall because analysts lack surrounding context. An isolated IP address rarely explains the full story.
Once integrating threat intelligence into CrowdStrike NG-SIEM becomes part of the workflow, every enriched alert carries supporting intelligence. Analysts immediately see associated malware families, threat actors, and historical campaigns linked to the indicator. The investigation moves forward faster.
-
Stronger detection engineering
Threat intelligence feeds also help detection engineers refine their rule sets.
When intelligence reveals new attacker infrastructure or behaviour patterns, engineers can quickly create new correlation rules inside NG-SIEM. These rules then watch for similar activity across the environment. Over time, detection coverage expands organically.
Emerging Trends Shaping Intelligence Driven SIEM Platforms
Security platforms are slowly shifting from log aggregation tools to intelligence driven analytics engines.
CrowdStrike’s NG-SIEM reflects this transition. Instead of operating purely as a data repository, the platform emphasises real time threat context across the detection pipeline. Several trends are shaping this shift.
Threat intelligence sharing between vendors is increasing. Intelligence platforms now aggregate data from multiple sources, including open-source research communities and commercial providers.
Machine learning models are also improving indicator validation. These systems help filter false positives within intelligence feeds before they enter the detection environment.
Another trend involves behavioural intelligence. Rather than relying solely on static indicators, intelligence providers increasingly track attacker tactics and infrastructure patterns. When these insights feed directly into SIEM platforms, detection becomes significantly more proactive.
This broader shift makes integrating threat intelligence into CrowdStrike NG-SIEM an important step for organisations seeking more contextual security operations.
Operational Considerations Before Implementation
Despite the benefits, intelligence integration still requires careful planning.
Not all intelligence feeds deliver equal value. Some contain large volumes of low confidence indicators that can increase alert noise. Security teams should prioritise curated intelligence sources with strong validation processes.
Data ingestion performance also matters. NG-SIEM environments must handle large data streams without slowing analytics performance.
Finally, security teams should make sure that intelligence enrichment integrates with their incident response workflows. Alerts should flow smoothly from detection to investigation and containment. Without this alignment, intelligence feeds risk becoming another disconnected data source.
Conclusion
Security data continues to grow across modern enterprise environments. Endpoints, cloud platforms, identity systems and network infrastructure generate constant streams of data. Without context, much of that information remains difficult to interpret.
Integrating threat intelligence into CrowdStrike NG-SIEM introduces the missing layer of context that security teams need. Intelligence feeds enrich data with known attacker infrastructure, campaign insights and behavioural indicators. Alerts become more meaningful, investigations become faster, and detection accuracy improves across the SOC.
Organisations that want to implement this approach often require specialised guidance to design the right intelligence pipelines and detection workflows. CyberNX can provide that guidance and give CrowdStrike consulting services that can help firms get full value from their Falcon platform. They help you design, deploy and manage Falcon in your environment – with 24×7 support and MDR to respond to threats anytime.
With the right integration strategy, threat intelligence becomes more than a data source. It becomes a practical advantage for modern security operations.



